what is XXE?
XXE (XML External Entity) vulnerabilities arise when an application processes XML input that contains a reference to an external entity. This vulnerability allows an attacker to exploit the system by reading local files on the server, triggering denial of service, or even performing SSRF (Server Side Request Forgery) attacks. At the heart of the XXE issue is the XML’s ability to define entities with external references, which can point to URI schemes or local resources, potentially leaking internal information.
In the realm of cloud platforms, such as OpenStack, the risk of XXE vulnerabilities can be amplified. Given that OpenStack manages various cloud-based resources, any XXE vulnerability within its ecosystem could lead to significant data breaches or disruptions in cloud operations.
Such vulnerabilities often originate from insecure parsing configurations or a lack of input validation when processing XML data. Moreover, as cloud platforms like OpenStack grow in complexity, the potential attack vectors for XXE exploitation may also multiply if not adequately addressed.
To defend against XXE attacks, especially in platforms like OpenStack, organizations need to ensure secure coding practices, emphasizing proper input validation and secure XML parsing configurations. Furthermore, regularly auditing and testing the software stack for potential XXE and other vulnerabilities can help in timely detection and mitigation, safeguarding the integrity of cloud operations and data.

To prevent XXE attacks, developers can implement secure coding practices, such as using a restrictive XML parser configuration or validating XML input against a schema. Additionally, web application firewalls and other security controls can help to detect and block XXE attacks.
Advisory
Vulnerability: XXE
Vendor: OpenStack
Module: nova
CVE: CVE-2021-29410
Version: 23.0.0
Severity: High
What Is OpenStack Nova?
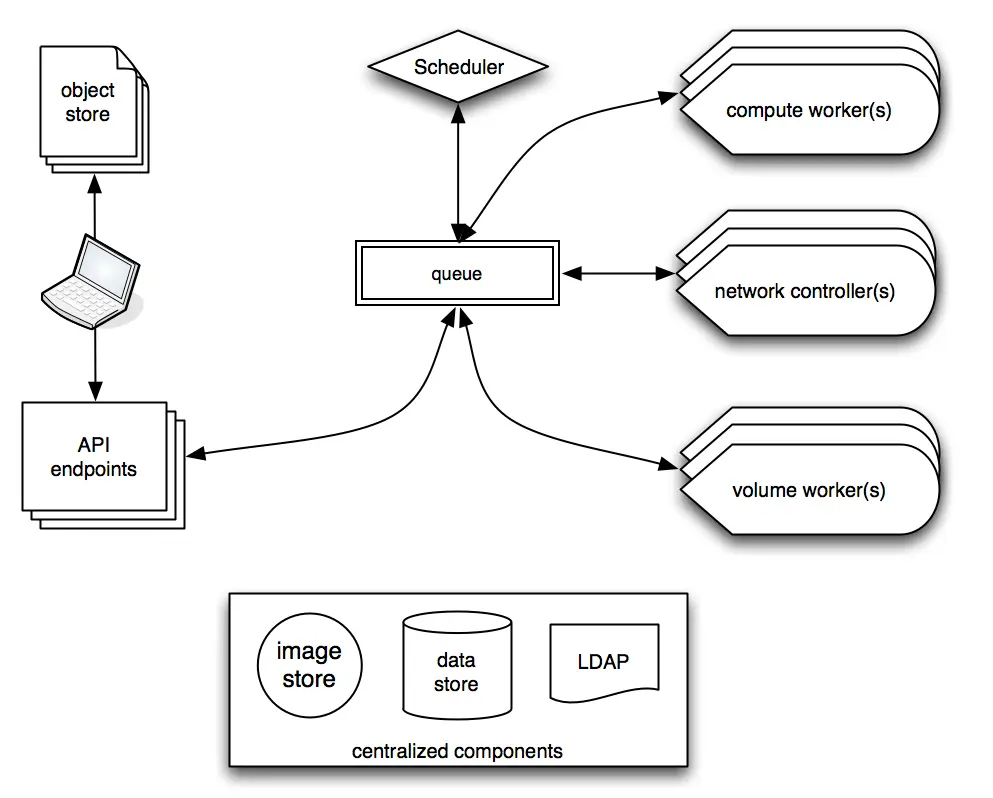
OpenStack Nova is a core component of the OpenStack cloud computing platform that provides virtual machines (VMs) as a service. It is responsible for managing and provisioning compute resources in the cloud, including creating, scheduling, and terminating VMs.
Nova is designed to be highly scalable and flexible, with support for multiple hypervisors, including KVM, Xen, Hyper-V, and VMware. It also includes a robust API that allows users to programmatically provision and manage VMs, as well as a web-based dashboard for easy management and monitoring.
Key Features Of Nova
Some of the key features of Nova include:
- Multi-hypervisor support: Nova supports multiple hypervisors, allowing users to choose the best option for their workloads.
- Autoscaling: Nova includes built-in support for the automatic scaling of VMs based on usage patterns and resource availability.
- High availability: Nova is designed to be highly available, with support for fault tolerance and automatic recovery in the event of a failure.
- Live migration: Nova supports live migration of VMs, allowing them to be moved between hosts without interrupting service.
- Security: Nova includes features such as network isolation and virtual machine introspection to enhance security in the cloud.
Overall, OpenStack Nova is a key component of the OpenStack cloud computing platform, providing a powerful and flexible way to manage and provision compute resources in the cloud.
Vulnerabilities
Root Cause
By default, the XMLParser in Python does not disable the use of external entities, which can make it vulnerable to XXE attacks. This means that if an attacker can control the contents of an XML document that is being parsed by Python’s XMLParser, they may be able to include an external entity reference that points to a file or resource on a remote system, and the XMLParser will process that external entity, potentially leading to a security breach.
For example:
XMLParser(self, encoding=None, attribute_defaults=False, dtd_validation=False, load_dtd=False, no_network=True, ns_clean=False, recover=False, schema: XMLSchema =None, huge_tree=False, remove_blank_text=False, resolve_entities=True, remove_comments=False, remove_pis=False, strip_cdata=True, collect_ids=True, target=None, compact=True)
Available boolean keyword arguments:
attribute_defaults – inject default attributes from DTD or XMLSchema
dtd_validation – validate against a DTD referenced by the document
load_dtd – use DTD for parsing
no_network – prevent network access for related files (default: True)
ns_clean – clean up redundant namespace declarations
recover – try hard to parse through broken XML
remove_blank_text – discard blank text nodes that appear ignorable
remove_comments – discard comments
remove_pis – discard processing instructions
strip_cdata – replace CDATA sections by normal text content (default: True)
compact – save memory for short text content (default: True)
collect_ids – use a hash table of XML IDs for fast access (default: True, always True with DTD validation)
resolve_entities – replace entities by their text value (default: True)
Vulnerable Code
nova/nova/virt/libvirt/migration.py
Here is an example of vulnerable code that uses the XMLParser in Python and is susceptible to XXE attacks:
| import xml.etree.ElementTree as ET xml_data = ”'<?xml version=”1.0″ encoding=”UTF-8″?><!DOCTYPE foo [<!ELEMENT foo ANY><!ENTITY xxe SYSTEM “file:///etc/passwd”>]><foo>&xxe;</foo>”’ root = ET.fromstring(xml_data) |
In this example, the XML data contains an external entity reference to the /etc/passwd file on the local system. When the XMLParser parses the XML data, it will resolve the external entity and include the contents of the /etc/passwd file in the resulting XML tree. This can potentially expose sensitive information to an attacker.
To prevent XXE attacks in this code, you can disable external entity resolution by passing a custom parser to the ET.fromstring() function, like this:
| import xml.etree.ElementTree as ET xml_data = ”'<?xml version=”1.0″ encoding=”UTF-8″?><!DOCTYPE foo [<!ELEMENT foo ANY><!ENTITY xxe SYSTEM “file:///etc/passwd”>]><foo>&xxe;</foo>”’ parser = ET.XMLParser(resolve_entities=False)root = ET.fromstring(xml_data, parser=parser) |
In this modified code, the resolve_entities parameter is set to False when creating the custom parser, which prevents external entities from being resolved. This effectively mitigates the XXE vulnerability in the original code.
To prevent XXE attacks in Python, you can use the defusedxml library, which provides a drop-in replacement for Python’s built-in XML libraries (including the XMLParser), with XXE protection enabled by default. You can install the defusedxml library using pip:
| pip install defusedxml |
Once installed, you can use the defusedxml library to parse XML documents with XXE protection enabled, like this:
| from defusedxml.ElementTree import parse tree = parse(xml_string)root = tree.getroot() |
Alternatively, you can disable external entities in Python’s built-in XMLParser by setting the resolve_entities parameter to False, like this:
| from xml.etree import ElementTree as ET parser = ET.XMLParser(resolve_entities=False)tree = ET.fromstring(xml_string, parser=parser) |
By disabling external entities, you can prevent XXE attacks in your Python code. However, it’s important to note that this may not be sufficient on its own, and other security measures may also be necessary to fully protect your application against XXE attacks.
XXE Mitigations
There are several ways to prevent XXE attacks, including:
- Use a restrictive XML parser configuration: Developers can configure the XML parser to disallow the use of external entities. This can prevent attackers from including malicious files or resources in the XML input.
- Validate XML input against a schema: Developers can validate the XML input against a schema that defines the structure and content of the XML document. This can help to ensure that the input is well-formed and does not contain unexpected or malicious elements.
- Use whitelisting: Developers can use a whitelist to explicitly allow only the expected XML elements and attributes to be processed by the application. This can help to prevent unexpected or malicious input from being processed.
- Filter user input: Developers can sanitize user input to remove any unexpected or potentially malicious characters or elements. This can help to ensure that the XML input is well-formed and safe to process.
- Implement web application firewalls: Web application firewalls can help to detect and block XXE attacks by analyzing incoming traffic and blocking any requests that contain suspicious or malicious input.
It’s important to note that preventing XXE attacks requires a combination of secure coding practices and security controls. Developers should also stay up-to-date with the latest security advisories and best practices to ensure that their applications remain secure. To learn more about Hadess, visit our website.