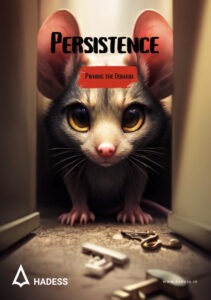
Pwning the Domain: Persistence EBook
Key findings from the “Pwning the Domain” series underscore the pervasive threat posed by attackers leveraging sophisticated techniques to exploit vulnerabilities within Windows domain environments. The series highlights the prevalence of persistence tactics, ranging from Group Policy manipulation and ticket-based attacks to the abuse of certificates and advanced techniques such as AdminSDHolder, GoldenGMSA, SID History, DC Shadow, Skeleton Key, DSRM, SSP, and methods for making users Kerberoastable. These findings underscore the urgent need for organizations to fortify their defenses, implement robust security measures, and prioritize proactive threat detection and mitigation strategies to safeguard against persistent threats in domain environments.
SIM Swap attacks EBook
SIM Swap attacks are well known to cybersecurity professionals. They allow an attacker to take control of the victim’s SIM card, enabling them to validate
Threat Intel Roundup: DARKGATE, TunnelVision, FIN7, OffensiveCon
Week in Overview(7 May-14 May) – 2024 it is crucial for organizations and individuals to prioritize remediation and patching efforts to safeguard their systems and
Threat Intel Roundup: Android, APT28, GHES, AMSI
Week in Overview(30 Apr-7 May) – 2024 it is crucial for organizations and individuals to prioritize remediation and patching efforts to safeguard their systems and
Pwning the Domain: Persistence EBook
Key findings from the “Pwning the Domain” series underscore the pervasive threat posed by attackers leveraging sophisticated techniques to exploit vulnerabilities within Windows domain environments.
SIM Swap attacks EBook
SIM Swap attacks are well known to cybersecurity professionals. They allow an attacker to take control of the victim’s SIM card, enabling them to validate
Threat Intel Roundup: DARKGATE, TunnelVision, FIN7, OffensiveCon
Week in Overview(7 May-14 May) – 2024 it is crucial for organizations and individuals to prioritize remediation and patching efforts to safeguard their systems and
Threat Intel Roundup: Android, APT28, GHES, AMSI
Week in Overview(30 Apr-7 May) – 2024 it is crucial for organizations and individuals to prioritize remediation and patching efforts to safeguard their systems and
Pwning the Domain: Persistence EBook
Key findings from the “Pwning the Domain” series underscore the pervasive threat posed by attackers leveraging sophisticated techniques to exploit vulnerabilities within Windows domain environments.
SAST
Expose secrets, misconfigurations, code mistake, and data breaches before they happen
E-Learning
interactive digital courseware designed to help development teams learn and implement best practices for secure coding
RASP
It's designed to detect and block attacks on applications in real time
Pwn ZO
Endpoint protection delivered as-a-service and backed with breach prevention warranty up to $1M
Hadess Red Team Operation
Flexible and Extensible
Each module below is available on the red team operation platform and its implemented via a single endpoint
Initial Access

PENETRATION TESTING
Endpoint Detection & Response
PRIVILEGE ESCALATION
Extended Detection & Response

SOCIAL ENGINEERING
Integrated Identify Security
Lateral Movement

DISCOVERY
Vulnerability Assessment

story2
story1
…